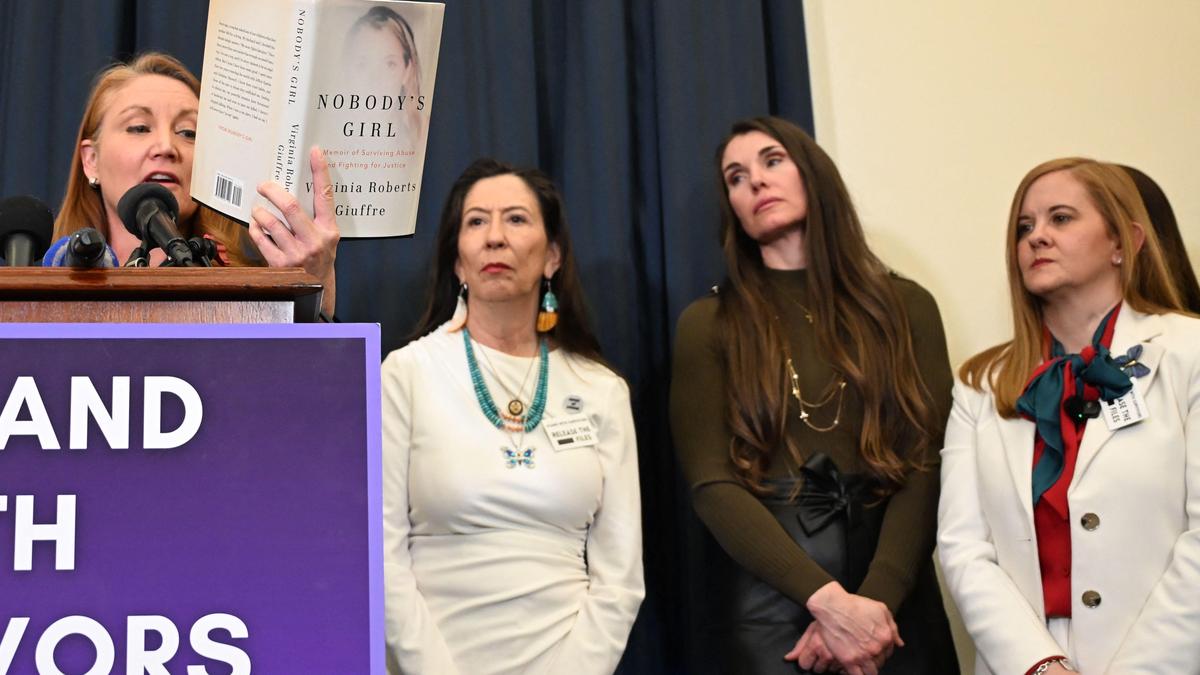
The failure to redact sensitive identity data in the Jeffrey Epstein litigation represents a systemic breakdown of the "privacy by design" principle, transforming a legal discovery process into a permanent digital exposure. When the U.S. Government and Google fail to synchronize data-masking protocols during the release of court documents, the resulting breach is not a temporary leak but an irrevocable shift in the risk profile of the affected individuals. This litigation, brought by survivors whose identities were exposed, centers on the intersection of sovereign immunity, third-party data hosting liabilities, and the technical mechanisms of "de-identification" that failed under the weight of public scrutiny.
The Triad of Institutional Failure
The exposure of protected identities in the Epstein files occurred across three distinct operational layers. Understanding the current lawsuits requires decomposing the event into these constituent failures:
- The Administrative Failure (Judicial Oversight): The court system relies on manual and semi-automated redaction processes. When a judge orders the unsealing of documents with specific caveats for "Jane Does," the execution falls to clerks and legal assistants. The failure here is one of granular verification—missing a single instance of a name in a 500-page PDF renders all other redactions in that document moot through "jigsaw identification."
- The Technological Failure (Incomplete Metadata Scrubbing): Digital documents carry layers of hidden data. In many instances of public record leaks, the visual layer is "blacked out," but the underlying text layer or the document’s metadata remains searchable. If Google’s indexing spiders crawl these documents before a correction is made, the data is cached and mirrored across the global web, making "deletion" a functional impossibility.
- The Custodial Failure (The Google Nexus): As the primary host and indexer of the world’s information, Google’s role shifts from a neutral tool to a liability-bearing entity when its algorithms prioritize high-interest, leaked sensitive data. The survivors' argument hinges on the "Right to be Forgotten" logic—or more accurately, the failure of a service provider to cease the distribution of harm once notified of a clerical error in a legal filing.
The Mechanics of Re-identification
The legal claim against the U.S. Government rests on the violation of the Privacy Act of 1974 and the Federal Tort Claims Act (FTCA). However, the technical catalyst is the "Re-identification Loophole." This occurs when a redacted document is compared against external datasets.
Even if a name is successfully obscured, a survivor’s identity can be reconstructed using:
- Temporal Markers: Dates of travel or specific meetings mentioned in the text.
- Geospatial Data: Specific locations or residential descriptions.
- Relational Mapping: References to "the assistant of X" or "the sibling of Y."
When the government releases these documents into the public domain via platforms like Google, they are essentially providing the "key" to an anonymous dataset. The "Mosaic Theory" of intelligence applies here: while no single piece of information is classified or protected, the sum of the parts identifies the individual. The survivors contend that the government had a "duty of care" to perform a mosaic analysis before the release, which they failed to execute.
Sovereign Immunity and the FTCA Bottleneck
A primary hurdle in suing the U.S. Government is the doctrine of sovereign immunity. To succeed, the survivors must navigate the Federal Tort Claims Act, which allows citizens to sue the government for certain negligent acts. The strategic challenge lies in the "Discretionary Function Exception." The government often argues that how it handles the release of court records is a matter of administrative discretion, not a mandatory, non-discretionary duty.
The plaintiffs’ counter-strategy focuses on the violation of specific, mandatory nondisclosure orders. If a judge issued a specific protective order for "Jane Doe 102," the failure to redact her name is no longer a "discretionary" policy choice—it is a direct violation of a court mandate. This removes the immunity shield and moves the case into the realm of standard negligence.
Google and the Section 230 Defense
The litigation against Google enters the contentious territory of Section 230 of the Communications Decency Act. Historically, platforms are not held liable for third-party content. However, the survivors' strategy targets two specific areas where Google’s immunity may fracture:
- The Amplification Variable: Google does not just "host" the documents; its algorithms actively rank and surface the most "relevant" (often the most scandalous) content. The argument is that Google’s algorithmic curation constitutes an editorial choice, moving them from "distributor" to "publisher."
- The Failure to Remediate: Once a court acknowledges a redaction error and a "take-down" request is issued, the persistence of cached versions or search snippets containing the exposed names becomes a deliberate act of distribution.
The Economic and Psychological Cost Function
The "damages" in these lawsuits are not merely emotional; they are quantifiable through a risk-assessment lens. The exposure of a survivor's identity in the Epstein case creates a permanent "Digital Tax" on the individual:
- Security Costs: The immediate need for digital footprint scrubbing, name changes, or physical security.
- Opportunity Loss: The "Google Search" barrier for future employment. An exposed identity creates a permanent association with a high-profile criminal case, leading to "reputational friction" in professional environments.
- The Persistence Factor: Unlike a physical leak, digital exposure has a half-life that approaches infinity. The value of the settlement must account for the "Present Value" of a lifetime of privacy loss.
Operational Redundancy as a Legal Standard
The core of the survivors' argument suggests that the standard for "reasonable care" in high-stakes litigation must evolve. A single-pass manual redaction is no longer sufficient. The proposed standard of care includes:
- Dual-Blind Redaction: Two independent teams redact the same document, and a third team identifies discrepancies.
- Algorithmic Verification: Using Natural Language Processing (NLP) to scan for PII (Personally Identifiable Information) that humans might overlook.
- Metadata Stripping: The forced removal of all non-visual data layers before a PDF is made public.
The failure to use these widely available tools constitutes a breach of the standard of care expected of a multi-billion dollar federal agency or a trillion-dollar tech conglomerate.
Strategic Forecast for Privacy Litigation
This case will likely serve as the "North Star" for future privacy litigation involving the intersection of government records and big tech indexing. If the survivors clear the motion-to-dismiss phase, it signals a shift toward holding tech platforms accountable for "algorithmic negligence"—the failure to suppress known, harmful, and erroneously released legal data.
For the U.S. Government, the outcome will likely force a massive overhaul of the PACER system and the administrative protocols for unsealing documents. The "manual check" is dead; the future of legal discovery must be programmatic.
Organizations and legal entities must immediately transition to "Immutable Privacy" protocols. This involves treating every document release as a potential data breach. The strategy moving forward is to implement a "Zero Trust" model for public record releases: no document is public-ready until it has passed both a manual legal review and a programmatic PII audit. For survivors, the legal path forward is not just seeking compensation, but forcing a judicial precedent that classifies PII in court records as "Critically Protected Infrastructure," making its accidental release a high-liability event for both the government and its digital distributors.